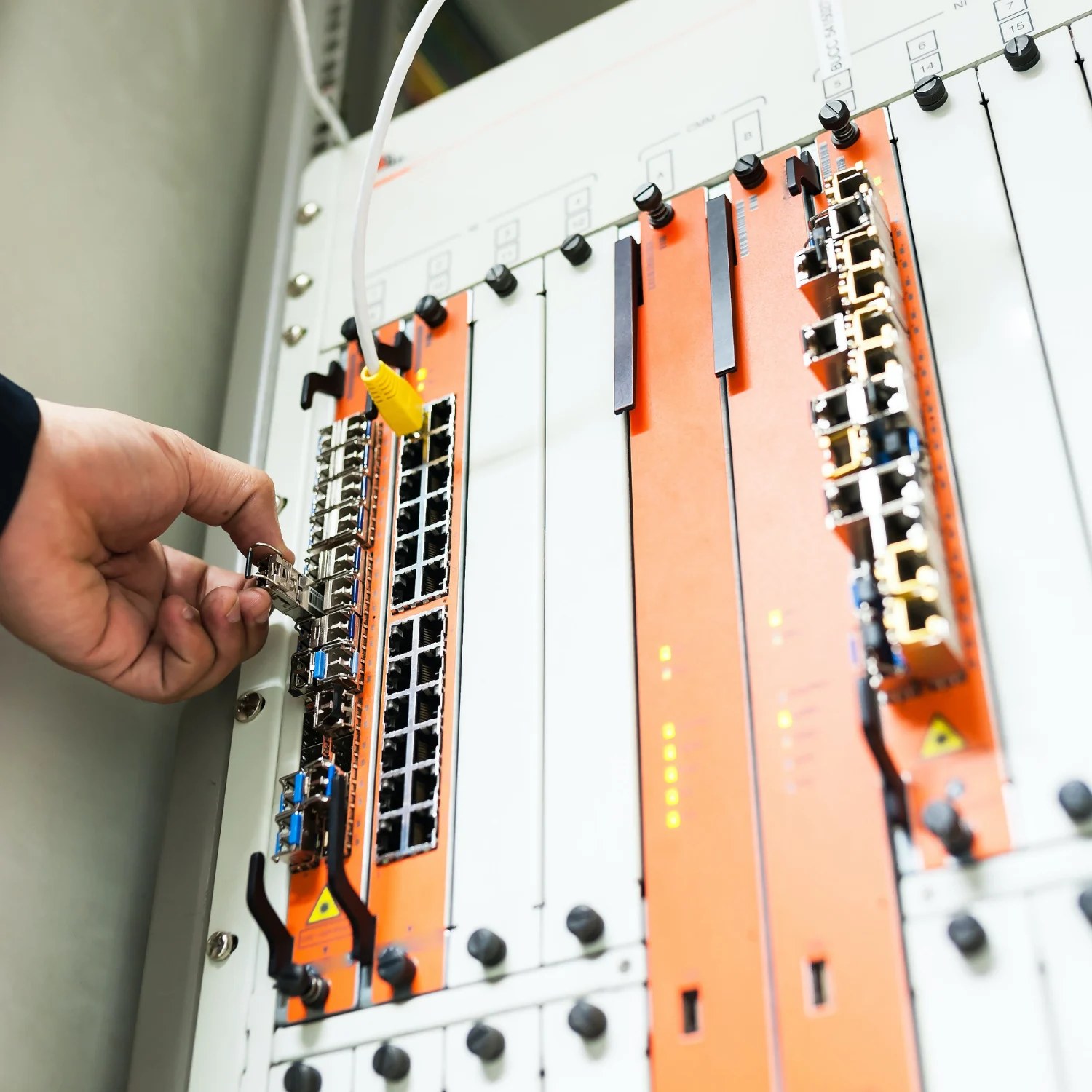
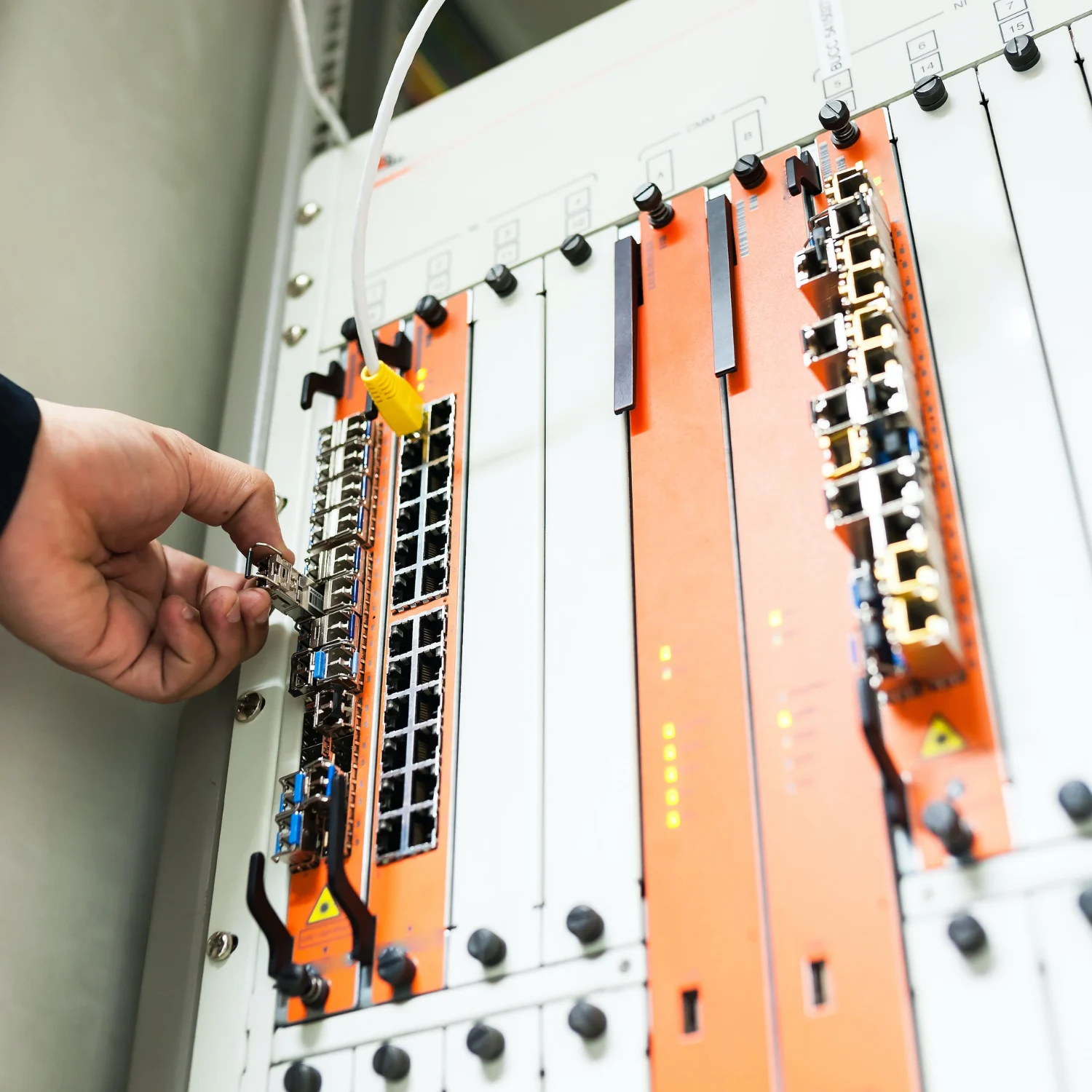
External and internal attack surface review for a distributed business
We assessed internet-facing assets, remote access paths, and internal segmentation to identify exploitable weaknesses, then verified remediation with a focused retest plan.
Simplified, anonymised security engagements focused on patterns, outcomes, and delivery quality rather than exposing client-sensitive detail.
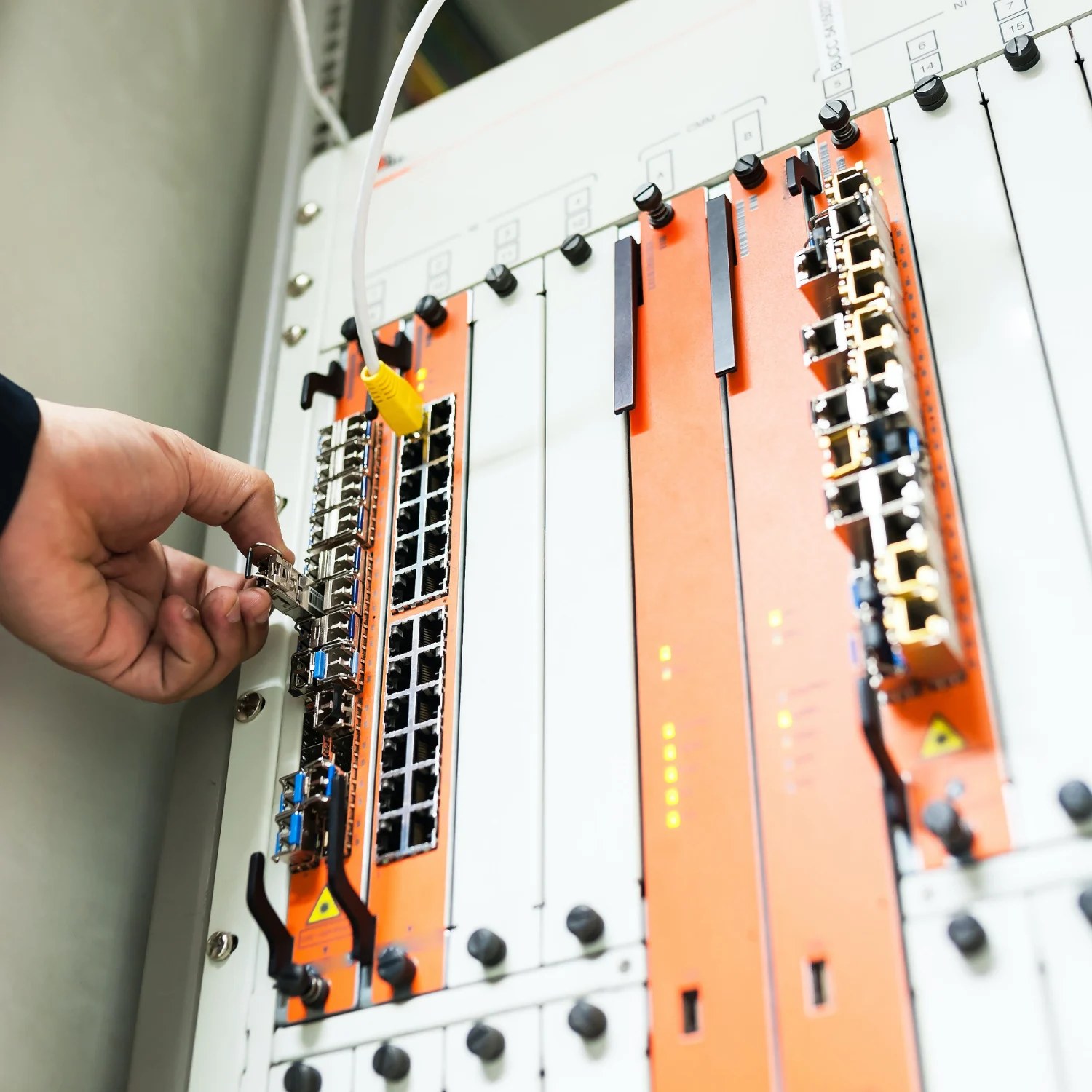
We assessed internet-facing assets, remote access paths, and internal segmentation to identify exploitable weaknesses, then verified remediation with a focused retest plan.

Identity, permissions, exposed services, and misconfigurations were reviewed and reduced through a phased hardening programme designed for a busy internal team.

We reviewed authentication, access control, logging, deployment controls, and app-layer risks before launch so the product went live with stronger security foundations.

A suspicious activity report turned into a structured DFIR engagement with timeline reconstruction, forensic collection, containment guidance, and post-incident recommendations.
We improved visibility, exposure handling, and defensive follow-through for a small team that needed a practical operating model instead of a heavy enterprise stack.

We designed and delivered focused internal tooling to speed up analyst tasks, structure findings, and reduce repetitive operational effort without adding platform bloat.

Suspicious binaries and scripts were analysed to understand execution patterns, persistence, network behaviour, and the indicators needed for containment and detection tuning.

We turned fragmented security concerns into a clearer roadmap, with phased priorities across governance, technical controls, testing, and engineering investment.